Preparing tech companies for today's risks
Resources for Technology
Navigating AI, Regulation and Rapid Change in Tech and Life Sciences
Explore how tech and life sciences companies can balance rapid innovation with evolving AI regulations. Watch insights from Travelers’ expert-led webinar.

Resources for Technology
Technology Mergers and Acquisitions: Key Risks and Opportunities
Explore how risk leaders can manage tech M&A challenges, from AI to integration. Travelers shares insights that guide success.

Resources for Technology
Semiconductor Supply Chain Challenges Impacting High Tech Manufacturing
Explore how high-tech manufacturers with global risks can navigate semiconductor supply chain issues amidst international unrest, weather workforce challenges and more.
Resources for Technology
Software Developers Beware of IT Risks from Semiconductors
Explore Travelers’ thorough findings on IT and semiconductor risks. Stay ahead in the fast-paced tech industry with expert guidance and proactive solutions.
Resources for Technology
Life Sciences Companies Face New Risks with Semiconductors
Semiconductors are essential for medical advancements, yet this reliance creates risks. Learn strategic insights to navigate complexities and ensure resilience.

Resources for Technology
Semiconductor Risks Facing Technology and Life Sciences
Explore Travelers’ insights and stay informed on semiconductor technology risks, including IT, electronic manufacturing, life sciences and telecom sectors.
Resources for Technology
How Telecommunications Businesses Manage Semiconductor Risks
Delve into Travelers’ analysis of semiconductor risks in telecommunications. Gain insights to mitigate potential challenges and ensure resilience in the industry.

Resources for Technology
3 Semiconductor Risks to Electronics Manufacturers
Semiconductors are essential to advanced electronics manufacturing, yet this reliance creates increased risks.
Resources for Technology
Managing the Risks of Artificial Intelligence
For technology and life sciences companies, AI offers exciting opportunities and potential risks. Learn the risks of artificial intelligence to these businesses.

Resources for Technology
A Large Price to Pay: Ransomware’s Urgent and Escalating Threats to Technology Companies
Technology and life sciences companies are at risk from ransomware because highly valuable intellectual property and consumer data make them prime targets.

Resources for Technology
4 Common Risk Challenges for Emerging Technology Companies
Explore the four common risk challenges emerging technology companies face and how they can better position themselves should something go wrong.

Resources for Technology
How Tech and Life Sciences Companies Can Capitalize on the AI Revolution and Manage the Risks
Reap the benefits while managing the risk of artificial intelligence. Learn how to mitigate risk while opening the door to pursue new opportunities with AI.
Resources for Technology
Medical and Healthcare IoT
The Internet of Things (IoT) is rapidly changing medical and healthcare technology. Here’s a look at some opportunities and risks for technology software developers, IT companies and manufacturers.

Resources for Technology
The Impact of Emerging Technology on Equipment
Learn how emerging technology is impacting equipment breakdown and five ways companies can prepare to be more resilient.

Resources for Technology
Tech Platform Companies and the Gig Economy Face New Risks
The gig economy is growing, but tech companies need to understand the emerging risks.

Resources for Technology
Supply Chain Technologies and How to Address Hidden Risks
Adding technologies to enhance current supply chain processes comes with risks and rewards. Learn how to address the risks.

Resources for Technology
The Risks of BYOD
Learn about the risks of BYOD and how to create a bring your own device policy for your business, along with BYOD employee training tips from Travelers.

Resources for Technology
Managing Your Intellectual Property (IP)
Managing intellectual property can help prevent unintentionally using unlicensed software. Learn more about intellectual property management from Travelers.

Resources for Technology
How High-Tech Manufacturers Can Prepare for Global Risks
Operating internationally brings new business risks, from global product liability to supply chain interruption. Learn about global risk management.

Resources for Technology
Defending Your Supply Chain from Counterfeit Electronic Parts
Help protect your supply chain against the risk of counterfeit electronic parts by knowing your suppliers and testing components. Learn more from Travelers.

Resources for Technology
5 Ways Public Entities Apply Smart Tech to Enhance Transportation
The technologies being deployed to improve transportation systems present public entities with new risks.

Resources for Technology
4 Technology Errors and Omissions Insurance Risks
Get smart on technology E&O coverage with these four items for tech companies to look for in the coverage.

Resources for Technology
The Risks of IoT in Medicine and Healthcare
From the smallest sensors to entire operating room systems, the Internet of Things (IoT) is helping to save lives and changing the practice of medicine.

Resources for Technology
5 Ways Cities, Municipalities and Other Public Entities Use Smart Tech for Public Safety
Smart streetlights and predictive policing are two ways smart technology is used for public safety. Explore smart tech for public safety.

Resources for Technology
Technology and Life Sciences Companies Face Unique Ransomware Risks
Learn how technology and life sciences companies face multiple impacts from ransomware attacks that can result in significant losses for technology and life sciences companies.

Resources for Technology
5 Tips for Choosing Workers Compensation Insurance for Tech Companies
Does your tech company have workers comp coverage designed for the unique needs of tech companies? It can be a competitive advantage. Learn how.

Resources for Technology
Managing Video and Social Media Policies for Law Enforcement Organizations
Videos and social media presents law enforcement with new risks. Here are five tips to help manage those risks.

Resources for Technology
5 Keys to Choosing Global Coverage for Tech Companies
High-tech companies are operating in a global business environment, which can mean unprecedented opportunities as well as new and evolving risks.

Resources for Technology
How Smart Cities Prepare for Technology Infrastructure Risks
Considering implementing smart city technology? Know the risks and how to help protect your public entity.

Resources for Technology
How to Help Protect Your Intellectual Property
Registering intellectual property (IP) and using written agreements can help protect intellectual property.

Resources for Technology
LED Lighting Risks of Maritime Radio Interference
LED lamps on smaller/coastal watercraft may cause electromagnetic interference, which can result in poor reception on VHF frequencies, according to a U.S. Coast Guard alert.

Resources for Technology
Safely Managing E-Waste
E-waste management, including electronic waste disposal, can help protect your business from counterfeiters.

Resources for Technology
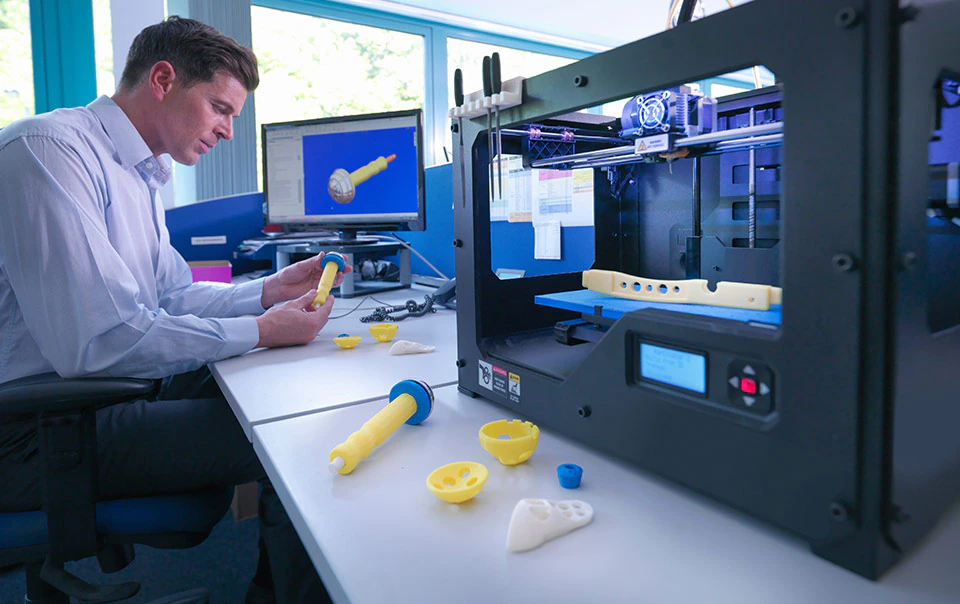
Preparing for the Risks of 3D Printing in Manufacturing
From property damage risks to intellectual property risks, learn four key risk categories for 3D printing that technology companies should understand.
Resources for Technology
14 Risks Facing Technology Companies and How to Help Protect Your Business
In the digital age, tech companies are often the backbone of their customers’ operations. Learn how Travelers insurance options can help tech companies add a layer of protection to their operations.

Resources for Technology
Ransomware: Tech Industry's Cyber Crime Wave
We explore tech companies' real-life ransomware stories, discuss ways to avoid becoming the next victim, and what should be in place to accelerate recovery if a breach occurs.

Resources for Technology
Protecting the Physical and Emotional Well-Being of Technology Industry Employees
From the new physical and procedural changes required to reopen and maintain healthy offices, to the social and emotional effects of working through the next phase of the pandemic, it’s safe to say that COVID-19 will have lasting effects on technology companies.